Cybersecurity Challenges in Connected Car Ecosystems
The evolution of the automobile has moved beyond mechanical engineering to embrace advanced digital technology, giving rise to connected car ecosystems. These modern vehicles offer enhanced safety features, improved navigation, and sophisticated infotainment systems, transforming the driving experience. However, this connectivity also introduces a complex array of cybersecurity challenges that demand careful consideration to ensure the safety, privacy, and reliability of future transportation.
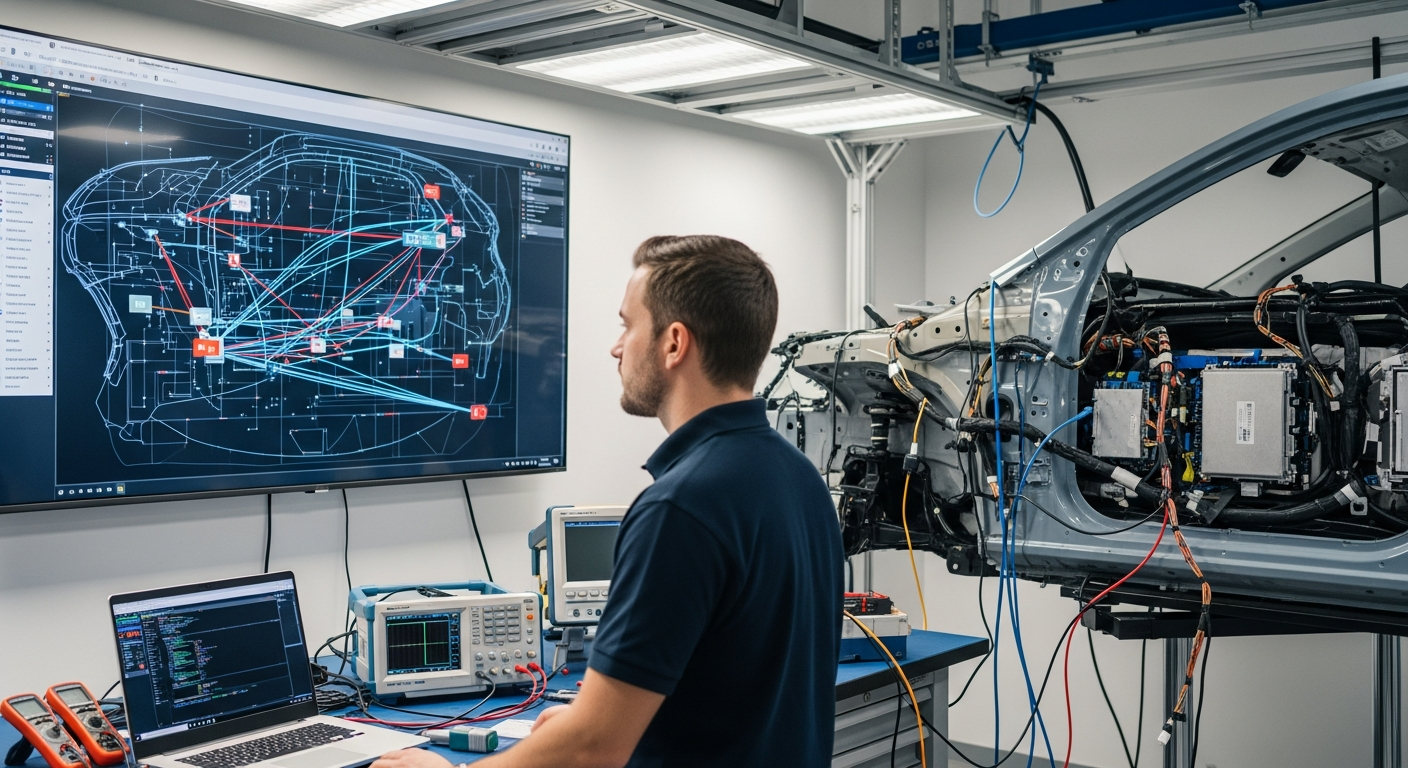
Understanding the Connected Vehicle Landscape
Connected vehicles are essentially data centers on wheels, integrating numerous electronic control units (ECUs), sensors, and communication modules. These sophisticated systems enable vehicles to communicate with other vehicles (V2V), infrastructure (V2I), the cloud (V2C), and pedestrians (V2P), collectively known as V2X communication. This extensive network connectivity brings significant benefits, from real-time traffic updates and remote diagnostics to advanced driver-assistance systems (ADAS) and the foundation for autonomous driving technology. The sheer complexity of these interconnected systems, however, creates a broad attack surface for potential cyber threats, making robust security measures critical for every automobile.
Data Privacy and Integrity Concerns in Mobility
Modern cars collect vast amounts of data, including driving patterns, location, personal settings, and even biometric information. Ensuring the privacy and integrity of this sensitive data is a paramount cybersecurity challenge. Unauthorized access to this information could lead to privacy breaches, identity theft, or even enable malicious actors to track an individual’s movements. Furthermore, the integrity of the data used by vehicle systems is crucial for safe operation. Compromised data could lead to incorrect navigation, faulty sensor readings, or manipulated engine controls, directly impacting the safety of the vehicle and its occupants. Robust encryption, secure data storage, and strict access controls are essential to protect this valuable information throughout its lifecycle, from collection to transmission and storage.
Vulnerabilities in Vehicle Communication Systems
The various communication channels within a connected car ecosystem present distinct vulnerability points. V2X communication, while offering immense potential for improving road safety and traffic efficiency, relies on wireless protocols that can be susceptible to eavesdropping, spoofing, or denial-of-service attacks. An attacker could potentially inject false information into a vehicle’s communication stream, causing it to misinterpret its surroundings or even trigger emergency braking unnecessarily. Similarly, vulnerabilities in cellular or Wi-Fi connections used for infotainment or remote services could allow unauthorized access to the vehicle’s internal network. Securing these external communication pathways is a significant challenge, requiring advanced cryptographic techniques and continuous monitoring to detect and mitigate threats effectively.
Software Updates and Supply Chain Security in Automotive Manufacturing
The software that powers connected vehicles is constantly evolving, necessitating frequent updates to introduce new features and patch security vulnerabilities. The process of delivering and installing these software updates securely is vital. If the update mechanism itself is compromised, malicious software could be inadvertently installed, giving attackers control over vehicle functions. Beyond software, the automotive supply chain involves numerous components and systems from various manufacturers. Each link in this chain can introduce potential security weaknesses, from compromised hardware during manufacturing to vulnerabilities in third-party software components. Ensuring end-to-end security across the entire supply chain, from design and manufacturing to deployment and ongoing maintenance, is a complex undertaking that requires collaboration among all stakeholders in the transportation industry.
Impact on Autonomous Driving Systems and Future Safety
As the industry progresses towards fully autonomous vehicles, the stakes for cybersecurity become even higher. Autonomous driving systems rely heavily on complex algorithms, real-time sensor data, and continuous connectivity to make critical decisions without human intervention. A successful cyberattack on an autonomous vehicle could have catastrophic consequences, potentially leading to accidents, loss of control, or even turning the vehicle into a weapon. Protecting the integrity of the AI and machine learning models, securing sensor inputs against spoofing, and ensuring the resilience of the decision-making systems are paramount. The future of mobility and the widespread adoption of self-driving cars depend heavily on the public’s trust in the impenetrable security of these advanced systems, making cybersecurity a foundational element of their design and operation.
Securing the Electric Vehicle Charging Infrastructure
With the growing adoption of electric vehicles (EVs), the charging infrastructure also becomes a critical component of the connected car ecosystem that requires robust cybersecurity measures. EV charging stations are increasingly networked, allowing for remote management, billing, and smart grid integration. Vulnerabilities in these systems could lead to unauthorized access to personal information, manipulation of charging schedules, or even broader disruptions to the power grid. Ensuring the secure communication between the electric vehicle, the charging station, and the utility grid is essential to prevent malicious activities that could impact the reliability and safety of electric transportation. This includes securing the communication protocols, implementing strong authentication mechanisms, and protecting against physical tampering of charging units.
Addressing the cybersecurity challenges in connected car ecosystems requires a multi-faceted approach, encompassing secure design principles, robust encryption, continuous monitoring, and collaborative efforts across the entire automotive and technology industries. As vehicles become more integrated into our digital lives, safeguarding these complex systems is not just about protecting data, but ensuring the safety and reliability of modern transportation for everyone on the road.






